Cyber Security Threats and How to Prevent Them
Modern business has been altered by growth of the Internet. Organizations are increasingly making news due to cyber security threats and how to prevent them. Organizations are increasingly making news due to cybersecurity breaches. Every year, these attacks cause damage to corporate networks, equipment, business processes, and data, costing companies billions of dollars in losses and missed opportunities. Today, firms must invest in deterrents to these cybersecurity dangers. Here are the top ten most common and costly cyber security threats today, as well as the actions a business may take to avoid them.
 Because it can be high-tech or low-tech, phishing is a widespread yet severe cyberthreat. Criminals act as genuine companies in these assaults to take advantage of victims’ trust, curiosity, greed, or charity. They send bogus emails in order to persuade their victims to submit sensitive information such as passwords, social security numbers, or bank account information.
Because it can be high-tech or low-tech, phishing is a widespread yet severe cyberthreat. Criminals act as genuine companies in these assaults to take advantage of victims’ trust, curiosity, greed, or charity. They send bogus emails in order to persuade their victims to submit sensitive information such as passwords, social security numbers, or bank account information.
Some of the most frequent phishing scam strategies used by hackers nowadays include:
- Spear phishing is the use of personalized messaging to target certain organizations or individuals.
- Pretexting is creating fictitious but realistic events in order to gain the target’s trust and obtain sensitive information.
- Mortgage fraud entails defrauding individuals by using stolen identities or fabricated income and asset data.
- Baiting is the use of enticing incentives or possible rewards to entice people to provide sensitive information.
- Pharming is the practice of redirecting website users to bogus websites that seem authentic in order to collect sensitive personal information.
- Whaling – Phishing assaults targeting an organization’s top leadership or high-profile workers, such as the Chief Executive Officer or Chief Financial Officer.
Cybercriminals who utilize phishing are very adept and frequently convincing. To deter such attacks, a business should train its personnel on how to recognize such attempts and invest in email filtering software to detect bogus websites and emails. They may also reduce these threats by requiring multi-factor authentication on all accounts and routinely updating their software with the most recent patches and upgrades.
Vishing (conducted via phone calls) and smishing (conducted via text messaging) are two further types of phishing.
 Social engineering assaults have been some of the most expensive cyber risks in history. Criminals use human psychology rather than technical weaknesses to deceive individuals into supplying sensitive information or access to data, networks, and systems. Social engineering assaults take many forms, ranging from phishing and luring to quid pro quo.
Social engineering assaults have been some of the most expensive cyber risks in history. Criminals use human psychology rather than technical weaknesses to deceive individuals into supplying sensitive information or access to data, networks, and systems. Social engineering assaults take many forms, ranging from phishing and luring to quid pro quo.
Today, organizations may take the following actions to protect themselves from social engineering threats:
- Learning about the most recent types of social engineering assaults and teaching staff to recognize their warning flags
- Restricting access to critical systems and information and evaluating permits on a frequent basis
- Scanning and blocking harmful emails and email attachments using email filters, firewalls, and anti-malware software
- Conducting frequent security audits and vulnerability assessments to uncover and address any security flaws in the business
- Using data loss prevention techniques to guarantee that data is not released in an unlawful manner
These preventative measures can help a company better defend itself against social engineering cyber attacks and protect its sensitive systems, information, and assets.
 Malware is an abbreviation for harmful software. As the name implies, they are computer programs that are meant to harm a computer system, network, or device. Malware may take many forms, from innocuous bothersome pranksters to deadly and sophisticated programs that can leave a whole computer system inoperable.
Malware is an abbreviation for harmful software. As the name implies, they are computer programs that are meant to harm a computer system, network, or device. Malware may take many forms, from innocuous bothersome pranksters to deadly and sophisticated programs that can leave a whole computer system inoperable.
Some of the most frequent types of malware are:
- Viruses on computers
- Rootkits
- Trojans
- Worms, bots, and botnets
- Malware without a file
- Adware Spyware
Using up-to-date antivirus and antimalware software is the most efficient technique to guard against malware. Using firewalls to restrict access to important systems and data adds another layer of virus protection. Users should also use caution when clicking on links in emails and downloading email attachments. Having a cybersecurity specialist do a vulnerability assessment on systems and networks may also assist firms in identifying any holes that malware can exploit.
 Ransomware attacks on corporations have grown so common in recent years that this virus has earned its own section. This is a sort of malware that encrypts computer files and then demands money to decrypt them. The FBI advises organizations against paying the ransom since there is no assurance that the thieves would release the material in the end.
Ransomware attacks on corporations have grown so common in recent years that this virus has earned its own section. This is a sort of malware that encrypts computer files and then demands money to decrypt them. The FBI advises organizations against paying the ransom since there is no assurance that the thieves would release the material in the end.
Ransomware attacks may be especially harmful for businesses that rely on data and cannot afford downtime.
Here are some steps that a company may take to defend itself from ransomware:
- Backup critical data on a regular basis to an offline or distant system.
- Distinguish between administrative (privileged) and normal (non-privileged) accounts.
- Use powerful anti-malware and anti-virus software that is up to date.
- Restriction of critical data and program access.
- Educate staff on how to recognize suspected phishing emails and how to use safe computer habits.
Ransomware is still one of the most dangerous dangers to companies today since it is extremely rewarding for criminals.
 Zero-day vulnerabilities are flaws in a computer system that can be exploited but are unknown. While it is uncommon for software products to include serious security holes, when they do, thieves might create tools to exploit them. Zero-day vulnerabilities are extremely dangerous because they allow hackers to circumvent existing security measures and gain unauthorized access to a computer system, network, or sensitive data.
Zero-day vulnerabilities are flaws in a computer system that can be exploited but are unknown. While it is uncommon for software products to include serious security holes, when they do, thieves might create tools to exploit them. Zero-day vulnerabilities are extremely dangerous because they allow hackers to circumvent existing security measures and gain unauthorized access to a computer system, network, or sensitive data.
Users and organizations should take the following precautions to avoid zero-day vulnerabilities:
- Keep their software up to date with the most recent fixes.
- Use heuristic (behavior-based) intrusion prevention solutions that can detect and block unknown attackers.
- Sandboxing technology may be used to isolate and study possible hazards.
- Control access to sensitive data, systems, and networks.
Every day, cybercriminals discover and exploit zero-day vulnerabilities. It is vital to be watchful and up to date on any new security measures necessary to guard against these attacks.
 Employees, contractors, and anyone having access to a computer system or network may do a lot of damage to a company. These risks might be unintentional or purposeful, and they can take several forms, such as causing system damage or exposing important data. our is one of the most hazardous threats on our list since it is difficult to foresee or detect.
Employees, contractors, and anyone having access to a computer system or network may do a lot of damage to a company. These risks might be unintentional or purposeful, and they can take several forms, such as causing system damage or exposing important data. our is one of the most hazardous threats on our list since it is difficult to foresee or detect.
An organization can take the following actions to defend itself from insider threats:
- Control access to sensitive systems and data.
- To avoid insider threats from angry workers, strive to cultivate a favorable business culture.
- Examine system and user logs to monitor user behavior.
- Install data loss prevention (DLP) solutions to reduce the impact of insider attacks.
- Perform background checks on all employees and contractors who have access to systems.
- Create an incident response strategy to lessen the effect of prospective assaults.
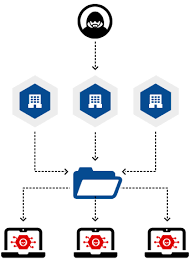 When an attacker uses a third-party supplier or vendor to get access to a target’s system, this is referred to as a supply chain attack. Malware infections and data breaches, as well as phishing and man-in-the-middle assaults, are examples of these attacks. In most situations, the attackers initiate the whole attack by first targeting a vendor or supplier with direct access to the organization’s systems.
When an attacker uses a third-party supplier or vendor to get access to a target’s system, this is referred to as a supply chain attack. Malware infections and data breaches, as well as phishing and man-in-the-middle assaults, are examples of these attacks. In most situations, the attackers initiate the whole attack by first targeting a vendor or supplier with direct access to the organization’s systems.
To defend against supply chain assaults, a company should:
- Perform thorough due diligence on third-party suppliers and contractors, as well as their cybersecurity measures.
- Install a security system for supply chain management.
- Keep track of all vendor actions on their system.
- Set security requirements that all suppliers must follow.
- Educate employees and staff on the significance of data security.
- Implement an incident response strategy to mitigate the effect of supply chain attacks.
 Denial of Service, or DoS, is a form of cyber attack that aims to flood an organization’s systems, website, or network with requests. This prevents genuine users from accessing the system or network. These assaults can take several forms, such as overloading the system with requests or exploiting system flaws.
Denial of Service, or DoS, is a form of cyber attack that aims to flood an organization’s systems, website, or network with requests. This prevents genuine users from accessing the system or network. These assaults can take several forms, such as overloading the system with requests or exploiting system flaws.
Denial of service assaults can have serious effects for businesses, including reputational harm, income loss, and even legal obligations. In certain circumstances, denial of service assaults serve as smokescreens for more serious attacks, such as data theft. The following procedures can be taken by an organization to protect itself from denial of service attacks:
- Put in place network security procedures.
- Use content delivery networks (CDNs) that are cloud-based.
- Provide DDoS mitigation services.
- Use rate limitation to test and uncover potential system or network vulnerabilities that attackers may exploit.
- Investing in more network traffic bandwidth to mitigate the effects of DDoS
 An unauthorized individual gaining access to a computer system or network is referred to as a system intrusion. Once in, the intruder may take data, cause damage to the system, or leave a backdoor for future assaults. An organization can avoid or lessen the impact of a system intrusion by doing the following:
An unauthorized individual gaining access to a computer system or network is referred to as a system intrusion. Once in, the intruder may take data, cause damage to the system, or leave a backdoor for future assaults. An organization can avoid or lessen the impact of a system intrusion by doing the following:
- Putting in place strict system and network access controls
- Keeping all software and systems up to date
- Conducting vulnerability assessments on a regular basis
- Using network segmentation to reduce the severity of intrusions
- Examining and monitoring network, system, and user records
- Employee education on appropriate cybersecurity measures to avoid social engineering
 A man in the middle cyber threat occurs when an attacker intercepts communication between two parties using specific tools. Chats or email communications between two users, or data between a user and a website server, are examples. The attacker listens in on the conversation in order to eavesdrop on or manipulate the information being communicated, frequently in order to steal sensitive information such as passwords and financial information.
A man in the middle cyber threat occurs when an attacker intercepts communication between two parties using specific tools. Chats or email communications between two users, or data between a user and a website server, are examples. The attacker listens in on the conversation in order to eavesdrop on or manipulate the information being communicated, frequently in order to steal sensitive information such as passwords and financial information.
Users may defend themselves from Man-in-the-Middle attacks by doing the following:
- Using encryption to safeguard network communications and data
- Validating digital certificates to guarantee that they are connecting with the appropriate recipient
- Being extra cautious when utilizing public Wi-Fi or falling victim to phishing assaults
- VPNs and data tunnels are used to safeguard data transferred and received.
 Today’s organizations confront a wide range of cyber security concerns. However, there are solutions to potentially lessen hazards and even secure computer systems, networks, and data for each threat. Using a comprehensive cybersecurity platform is one method to safeguard a company from all of these risks.
Today’s organizations confront a wide range of cyber security concerns. However, there are solutions to potentially lessen hazards and even secure computer systems, networks, and data for each threat. Using a comprehensive cybersecurity platform is one method to safeguard a company from all of these risks.
We at GauravGo also provide a safe hosting with full security.
Learn more about the various hosting services offered by GauravGo! We also provide a variety of offerings. So, follow us to stay up to date.
We’re here to help you get the most out of your hosting experience! We endeavor to give our clients with the greatest possible user experience as well as a variety of hosting options tailored to their unique requirements. With our unrivaled hosting services, designed exclusively for startups and students. Everyone will receive one month of free hosting and a subdomain, as well as up to 75% more low-cost hosting servers and a 3X easier-to-use interface with personalized customer support.
Please visit our website for further information.
Until then, be informed and safe.
